1. Define Your Surveillance Goal for your micro-spy A Micro-spy is a very powerful tool, but you need to know how to work with that. Choosing the right spy device might seem challenging, but with the right guidance, you can find the perfect tool for your surveillance needs. Whether you’re
Category: Technology
Laser Microphones
Can Spy On: Anybody with a window. How It Does It: Here’s the thing about “bugs,” even if they’re attached to living cockroaches. They have to emit radio waves in order to transmit their signal back to the listeners, which means they’re pretty easy to detect. With the right tools
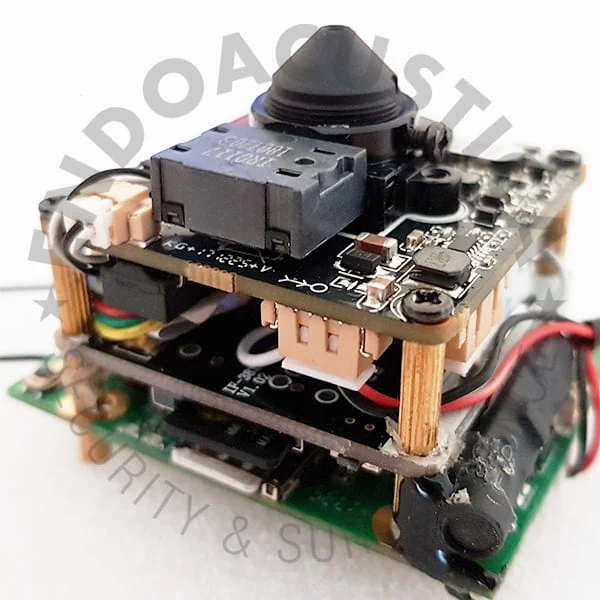
CCTV Systems
Nowadays, video cameras have become one of the most common things used by many people. Different people use them for different purposes. Some people use cameras while enjoying with their families & to capture those memorable moments; whereas, some people use them for security purpose. Today, security being one of
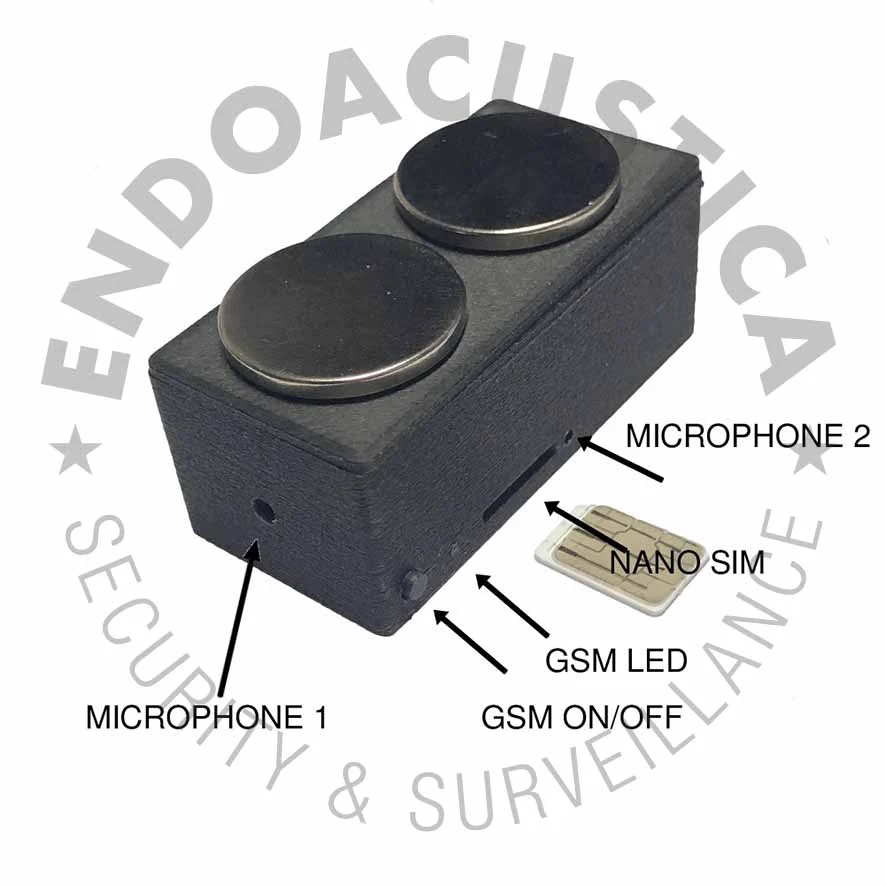
Hi-Tech Spy Equipments
In this hi-tech era, whether you have to monitor your employees in the office or to inspect your children’s mobile phone that what are they doing, spy surveillance system must be required for the monitoring. In this competitive era, no one has enough time to monitor their employees as well
Spy Technology – Top 5 Gadgets Available to the Public
Throughout the years, there have been many dazzling bits of spy technology that have wowed the crowds and left them wondering, “what if that was possible?” In many cases, this equipment has become a reality and is available in stores and online to any customer willing to make the purchase.
Total protection from eavesdropping, thanks to the invisible mobile phone
Since the beginning of time, men have always been dreaming about being able to fly, being invisible or talk freely wherever they are without anyone else listening, Unfortunately, as far as the first two dreams are concerned, your blogger is not able to assist, but he can surely give you
A spy phone will protect your children
Any parent knows that, during the age of growth, our kids’ curiosity, and their natural ingenuity which makes them trust anyone, may expose them to serious danger, for example when meeting people who, behind a respectable face, turn out to be real monsters. Unfortunately it is not always possible to
GPS Puzzle Box: It started out as a wedding gift…
It was originally born as a wedding present from a university researcher who wanted to surprise his friends, but GPS Puzzle Box, in fact, could have a potential for many more applications in several fields. It is a real modern version of the “treasure box” we read about in many
A GPS locator specifically designed for kids, to track them down anytime
For concerned parents, worried at the idea that their pre-teen kids might end up in trouble due to their natural curiosity and penchant for exploration, Brick House Security has just created Amber Alert, a small GPS sensor, practical and easy to use, which gives concerned parents the opportunity to know
Are you afraid of burglars while you are away on holiday? Film them!
Between hotels which do not live up to our expectations and unexpected rainstorms in midsummer, our holidays are not always as heavenly as we plan them. And if on top of all this, we have the unpleasant surprise of finding our home visited by burglars, that would really be the